// post · 579
Juniper SSG 5
We'll I finally got my new Juniper SSG 5 firewall (the replacement model for my old Netscreen 5gt).
I ordered it back in November, originally I was going to get the wireless version but they were still out of stock early this year so I ended up getting the base model (with 256mb of ram).
The main reason for the upgrade was that we'd run out of VPN tunnels (the 5gt did 10). The new version supports 25, plus it upgradeable to 40.
The SSG also has the following advantages over the 5gt (I'm comparing the base model 5gt and SSG 5):
- 4000 sessions, up from 2000
- 25 VPN tunnels, up from 10
- Unlimited users, up from 20 (my 5gt has an upgrade to support 20 users)
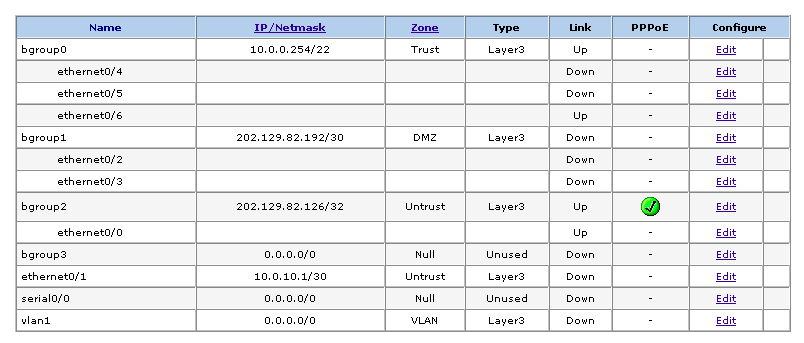
- 7 ethernet interfaces, up from 5 (plus they aren't limited in terms of zones like the 5gt).
- DMZ support (we've just got a subnet so this should be useful)
- Support for ScreenOS 6 which should be out this year
- Faster (160mb firewall (from 75mb), 40mb VPN (from 20mb))
- 256mb Ram, up from 128mb
- 64mb Flash, up from 32mb
So the device is pretty much double everything that the 5gt is.
It also cost me double. I got the 5gt off ebay for $320, where as the SSG 5 new cost me $640. I got a really good price on it has Bryn was able to sign up as a Juniper reseller, the SSG 5 is about $1200 retail.
The main limitation of the old Netscreen 5gt was the port modes.
The port mode defines what zone (untrust, trust, dmz etc) each ethernet interface is in. Any time you needed to change this you were required to reset the device and config (see below).
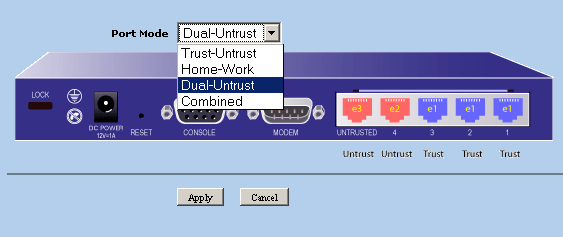
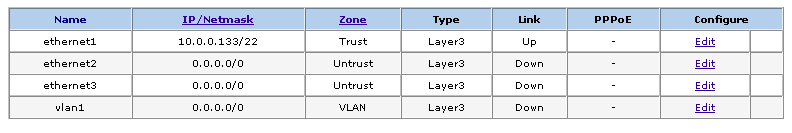
Where as the SSG 5 has something called bridge groups allowing you to easily change what zone each interface is in without resetting the device and/or config.
Much more useful if you're playing round with different network topologies (see below).
I've updated some of the IPSEC benchmarks to include both the SSG 5 and an old Netscreen 100 I picked up.
// leave a comment
HTML allowed: <a href="" title="" rel=""></a> <b></b> <blockquote cite=""></blockquote> <em></em> <i></i> <strike></strike> <strong></strong> <li></li> <ol></ol> <ul></ul>
ie: <b>bold</b>
Your comment may need to be reviewed before it is published.
// comments
The SSG 5's seem to be capable of full-blown NSRP, too, which blows HA Lite out of the water. I think you have to manually set the interface, though (ie, set nsrp int e0/4), instead of moving an interface into the HA zone.
Bets on when Juniper is going to EoL the 5GT/5GT-Wireless models?
I was a SunRocket customer and recently ran to Packet8. It took me a bit of fiddling to get the SSG-5 to play nice with traffic destined for the Packet8 VOIP ATA which I've setup in my DMZ using a VIP. If anyone is interested, I can post what I did.
Thanks!
Russ
sales@dinettemart.com